A new malware campaign is spreading a cryptocurrency miner called SilentCryptoMiner, hidden within software marketed as a tool to bypass internet restrictions. This deceptive tactic is part of a growing trend where cybercriminals use Windows Packet Divert (WPD) tools to distribute malware under the guise of helping users access blocked online services.
According to cybersecurity experts at Kaspersky, the malicious software is often packaged as archives with installation instructions that encourage users to disable security measures, falsely claiming that antivirus programs might flag it as a false positive. This trick helps the malware evade detection, allowing attackers to maintain control of infected systems without raising alarms.
Kaspersky’s researchers, Leonid Bezvershenko, Dmitry Pikush, and Oleg Kupreev, explained that this method has been employed in distributing various types of malware, including stealers, remote access tools (RATs), and cryptocurrency miners like NJRat, XWorm, Phemedrone, and DCRat.
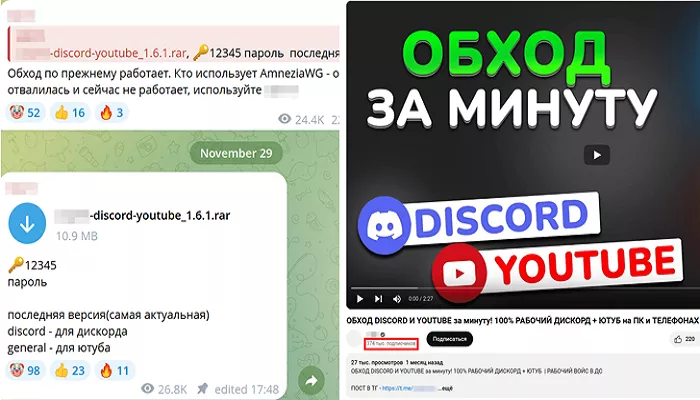
The latest wave of this campaign has targeted over 2,000 Russian users, who were tricked into downloading the miner, disguised as a tool for circumventing internet restrictions caused by deep packet inspection (DPI). The malware was shared through a link to a malicious archive on a popular YouTube channel with 60,000 subscribers.
In a disturbing escalation of tactics observed in late 2024, attackers began impersonating developers of these bypass tools. They threatened YouTube channel owners with fake copyright strikes, pressuring them to upload videos containing malicious links to avoid channel shutdowns.
Kaspersky noted that, in December 2024, reports surfaced about the distribution of an infected version of the tool via other Telegram and YouTube channels, which have since been taken down.
The malware-laden archives were designed to install a Python-based loader that downloads SilentCryptoMiner and ensures it runs persistently on the system. To bypass antivirus defenses, the installer includes a modified script that forces the user to disable their security software. If antivirus programs interfere with the attack, the user is shown an error message, prompting them to re-download the file and run it after disabling their protection.
SilentCryptoMiner is based on the open-source XMRig miner but has been modified to make detection more difficult. The malware includes random data blocks that artificially inflate its size to 690 MB, making it harder for antivirus solutions to analyze. Additionally, it uses a technique called “process hollowing” to inject itself into a system process (specifically dwm.exe), further hiding its presence.
To maintain a low profile, the miner halts its operation when specified processes are running and can be controlled remotely via a web panel.